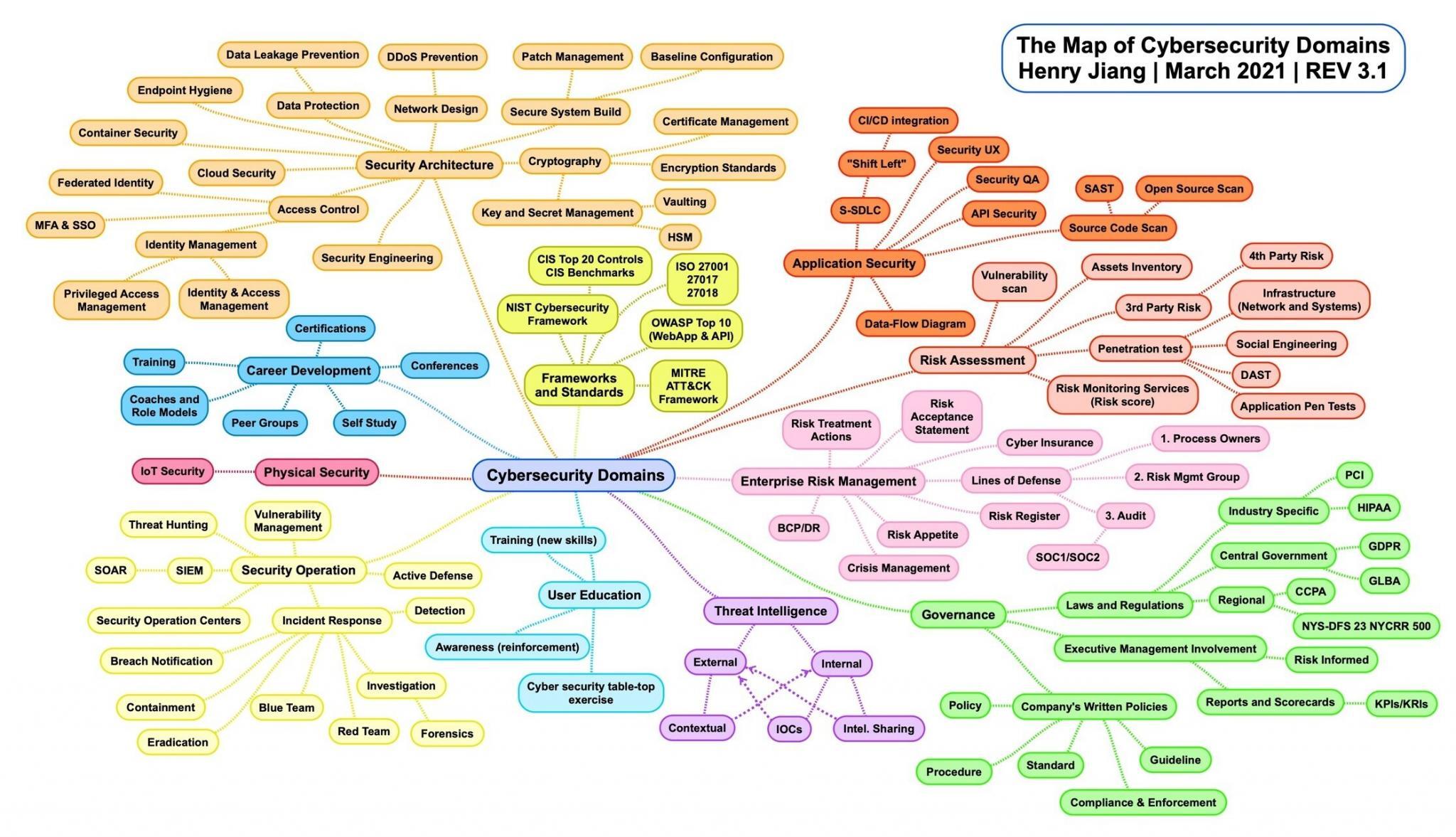
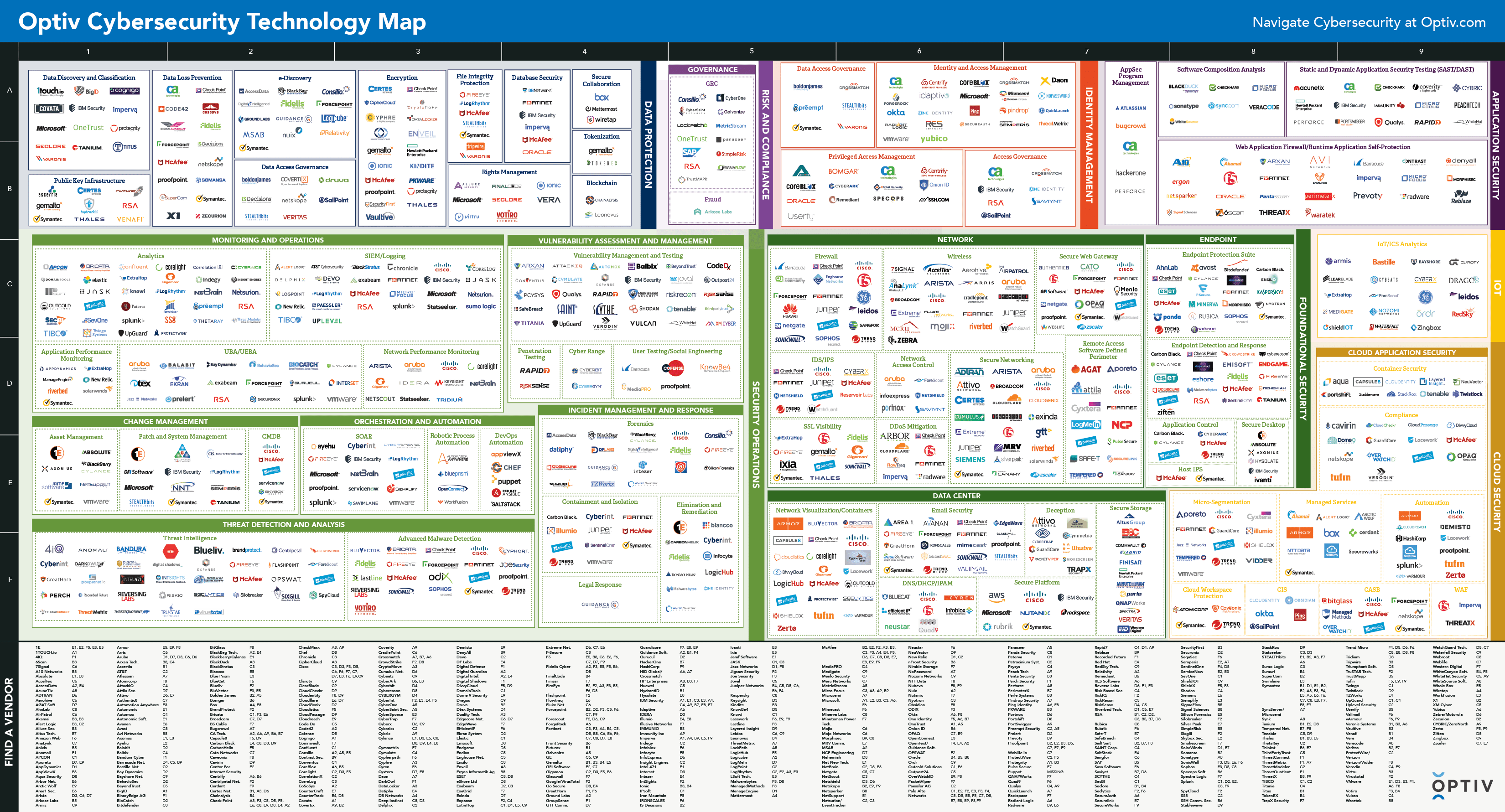
Last update images today Map Of Cybersecurity
Happ Slugs Pair Of 3-run Homers As Cubs Pound Phillies 10-2
SAN FRANCISCO -- Buddy Hield is joining the Golden State Warriors in a sign-and-trade deal with the Philadelphia 76ers that guarantees him two years and $21 million, sources told ESPN's Adrian Wojnarowski on Thursday.
Hield will receive $18 million in the first two years and a $3 million partial guarantee for 2026-27 as well as a player option for a non-guaranteed fourth year, sources said.
Golden State is sending Philadelphia a 2031 second-round pick it received from the Dallas Mavericks in the Klay Thompson sign-and-trade.
Pairing Hield with Stephen Curry will give the Warriors the top two 3-point scorers over the past five seasons. Hield is a 40% 3-point shooter in his career.
Hield is part of the Warriors' attempt to fill the void Thompson leaves as he heads to Dallas after 12 years with Golden State. The Warriors have also signed De'Anthony Melton and Kyle Anderson, giving the team decent versatility on both ends of the floor.
Last season, Hield played a league-high 84 regular-season games for the 76ers and Indiana Pacers. He averaged 12.1 points, 3.2 rebounds and 2.8 assists in 25.7 minutes per game. Hield struggled with his shooting in the playoffs outside of hitting six 3s in the 76ers' season-ending loss to the New York Knicks in Game 6 of their first-round series.